bitcoin’s Immutable Blockchain: Records Cannot Be Altered
bitcoin’s blockchain is a distributed, public ledger that records every transaction in a sequence of linked blocks. Each block contains a set of transactions and a cryptographic fingerprint that ties it to the previous block, creating an auditable chain of records that any participant can inspect. This ledger architecture is a foundational feature of bitcoin: by design it makes ancient transaction data obvious, verifiable, and resistant to unilateral changes .the practical immutability of bitcoin’s records arises from a combination of cryptography, economic incentives, and decentralized consensus. Transactions are secured with cryptographic proofs, blocks are produced through Proof-of-Work mining that requires notable computational effort, and the network accepts only the longest valid chain according to predefined consensus rules. Because altering a confirmed block would require redoing large amounts of work and convincing a majority of distributed nodes to accept the altered chain, past records become effectively irreversible under normal network conditions . This combination of technical mechanisms and network decentralization is what underpins claims that bitcoin’s blockchain cannot be altered.
Understanding bitcoin immutability and how transaction finality is achieved
Cryptographic linkage and distributed verification make past bitcoin records exceedingly difficult to alter. Each block contains a cryptographic hash of the previous block and a Merkle root summarizing all transactions; changing one transaction requires recalculating hashes and redoing the computational work for every subsequent block. This cost is enforced by bitcoin’s proof-of-work and the network’s consensus rules, so the practical barrier to rewriting history is both technical and economic. Key contributors to immutability include:
- Hashing: chaining blocks so changes cascade
- Proof-of-work: high computational cost to re-mine blocks
- Decentralization: many autonomous validators rejecting invalid history
- Full-node validation: nodes enforce consensus rules
Transaction finality on bitcoin is probabilistic rather than absolute: each new block that confirms a transaction increases the likelihood that the transaction will remain part of the canonical chain. Wallets and exchanges commonly use confirmation thresholds (for example, six confirmations) as a practical standard for confident finality, as the odds of a triumphant reorganization drop rapidly with depth. The following simple table summarizes the intuitive relationship between confirmations and reorg risk:
| Confirmations | Relative Reorg Risk |
|---|---|
| 0-1 | Higher |
| 2-3 | Moderate |
| 6+ | Low |
Trade-offs and governance are intrinsic to immutability: preserving an unchangeable ledger strengthens censorship resistance and trust, but it also makes protocol evolution and emergency fixes difficult because broad agreement is required to alter historic behavior. This tension-between strict immutability and the desire for adaptation-drives ongoing community debates about bitcoin’s future and upgrade processes. The resilience of finality and immutability ultimately rests on economic incentives, miner behavior, and social consensus among participants rather than on any single actor or institution .
Consensus mechanisms and proof of work as the foundation of irreversible records
Consensus mechanisms are the protocol-level rules that let a distributed network agree on one history of events without a central referee. In bitcoin, that agreement is achieved through a competition to produce proof of work: participants expend computational effort to add a block, and the network accepts the chain with the most accumulated work as canonical. This decentralized decision process is what prevents unilateral rewriting of history-no single participant can change past records unless they can overcome the combined work of the honest majority, a property central to blockchain security .
The practical mechanics that make records effectively irreversible combine cryptographic linking with economic cost. Each block contains a cryptographic hash of the previous block, so altering one block requires recomputing every subsequent proof of work; the network’s difficulty adjustment and the ongoing race among miners make re-mining a long chain prohibitively expensive. Key elements include:
- Cryptographic hashing – links blocks so a small change breaks the chain.
- Difficulty and work – force real resource expenditure to create a valid block.
- Longest/most-work chain rule – the network converges on the chain with greatest cumulative work.
- Economic disincentives - attacking the chain requires vast compute and costs, often exceeding potential gains.
Thes mechanisms operate together so that, while immutability is technically probabilistic, it becomes functionally irreversible after sufficient confirmations .
In practice this yields clear trade-offs and guarantees: security through costliness, but at the expense of throughput and energy. The table below summarizes how core PoW features map to irreversibility guarantees, making the concept tangible for operational risk assessment and design decisions.
| Feature | Role in Making Records Irreversible |
|---|---|
| Hash linking | Creates tamper-evident chains |
| Proof of work | Imposes high cost to rewrite history |
| Network consensus | Rewards the chain with most collective work |
Even though a 51% attack remains a theoretical risk, the combination of cryptography, distributed verification, and sustained economic cost renders bitcoin’s ledger effectively immutable for nearly all practical purposes .
Cryptographic hashing and Merkle trees explained for immutable data verification
Cryptographic hashes convert arbitrary transaction data into fixed-size digests that are easy to verify but infeasible to reverse. Thier core properties – one-way, deterministic, fixed-length output and the avalanche effect (small input changes produce large, unpredictable hash changes) – make them the building blocks of tamper-evident systems.
- One-way: you cannot recover original data from the hash.
- Collision resistance: finding two different inputs with the same hash is computationally infeasible.
- Fast to compute: verification is inexpensive compared to discovery.
Merkle trees organize many hashes into a single compact summary: leaf nodes hold hashes of individual data blocks (for example, transactions), and each parent node holds the hash of its children’s concatenated hashes. Repeating this up the tree produces a single Merkle root that cryptographically represents the entire dataset. As any modification to a single leaf changes only the hashes along the path to the root, verifying a single transaction’s inclusion requires only a small set of sibling hashes rather than the full dataset, enabling efficient integrity checks and compact proofs of inclusion.
In bitcoin, the Merkle root of a block’s transactions is recorded in the block header and secured by proof-of-work; altering any transaction forces recomputation of the affected hashes and the block’s PoW, and then every subsequent block’s PoW, making retroactive changes economically impractical. Lightweight (SPV) clients use compact Merkle proofs to confirm transaction inclusion without downloading full blocks, while full nodes use the chain of block headers and Merkle roots to detect any tampering.
| Component | Role |
|---|---|
| Merkle Root | Compact fingerprint of all transactions |
| merkle Proof | Log-sized inclusion proof for a transaction |
| Block Header | Anchors Merkle root with PoW to make tampering costly |
Practical techniques to independently verify bitcoin transaction integrity
Inspect the transaction on a public explorer to obtain the txid, raw hex, block inclusion and confirmation count – these are the first signals of integrity you can check without trusting a counterparty. Use a reputable explorer to view the exact outputs, input addresses, block height and the number of confirmations; mismatches across explorers or missing block references are red flags.
- Transaction ID (txid): confirm it matches what the sender provided.
- Confirmations: more confirmations increase immutability.
- Raw hex / script details: inspect inputs, outputs and scriptPubKey if available.
Practical explorer examples and step-by-step lookup instructions are widely documented for bitcoin verification tasks and in user guides that explain how to read transaction fields .
prefer a full node for definitive validation: an SPV (lightweight) wallet can prove that a transaction is included in a block, but it cannot independently validate whether the transaction itself respected all consensus rules; only a full node fully verifies scripts, signatures and consensus history. To independently verify integrity you can (1) obtain the raw transaction hex, (2) fetch the block header and merkle proof for the containing block and (3) compute the txid and merkle root to confirm inclusion – steps that a full node performs locally. The practical difference between SPV and full-node validation and why running a full node gives stronger guarantees is explained in bitcoin Core’s validation documentation and implementation guides .
| Quick check | How to do it | What it ensures |
|---|---|---|
| Confirmations | Check explorer / node | Finality increases with more blocks |
| Block inclusion | Merkle proof or explorer claim | shows transaction was included in a specific block |
| Raw tx match | Compare hex or txid | Detects tampering or substitution |
Best practice: cross-check the txid and block details on multiple explorers and, when possible, validate using your own node (or obtain a merkle proof from a trusted full node) to remove third-party trust. Community guides and explorers offer practical tools for these checks .
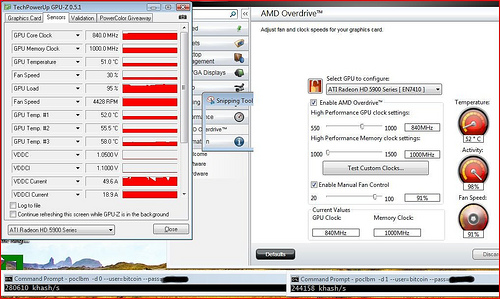
Recommended node setup and maintenance for reliable immutability confirmation
Run a dedicated full node whenever possible - a local copy of the entire bitcoin blockchain is the definitive way to confirm immutability without trusting third parties. Recommended minimums:
- CPU: 4 cores (modern x86 or ARM)
- RAM: 8-16 GB
- Storage: 1 TB NVMe for archival; 500 GB NVMe for pruned setups
- Network: 100 Mbps symmetric with a static IP or dynamic DNS
- Power/resilience: UPS and daily off-site backup of wallet and config
These choices minimize I/O bottlenecks and reduce the chance of data corruption, ensuring your node can validate headers and full block data to independently confirm that historical records remain unchanged.
Routine maintenance keeps immutability checks reliable: keep bitcoin Core (or your chosen implementation) updated and verify release signatures before upgrading; periodically run validation/reindex operations after major upgrades; monitor disk SMART data and filesystem integrity; and use automated alerting for stalled sync, excessive orphaned blocks, or unusual fork activity. For cross-validation, operate at least two independent nodes (different machines or cloud/on-prem split) and, if practical, run an choice implementation alongside bitcoin Core to detect client-specific bugs. Below is a compact operational cheat-sheet for common node roles:
| Node Type | Primary Use | Approx. Storage |
|---|---|---|
| Archival | Full audit & historical lookup | 1+ TB |
| Pruned | Fast validation, lower storage | ~50-500 GB |
| Watch-only/Relay | Monitoring & propagation | 10-50 GB |
Operational security and confirmation practices determine whether the immutability you observe is trustworthy in practice: always verify binary signatures for client updates, restrict RPC access with strong credentials and firewall rules, and consider Tor or VPN for peer privacy. During periods of high market stress or rapid price moves – when reorg attempts or chain-split risks are most consequential – rely on your local node (not public explorers) to confirm block depth and header-chain continuity; independent verification is especially valuable when network conditions change rapidly. For operational decisions tied to value exposure, reference price and liquidity data sources as context but not as a substitute for on-chain verification (live market info: ).
Common threats to perceived immutability and how to mitigate them
Technical and human weaknesses can give the false impression that bitcoin’s blockchain can be altered. Common threats include:
- 51% / majority-hash attacks: if an attacker controls a majority of mining/validation power they can reorganize recent blocks and double-spend transactions - a low-probability but high-impact vector linked to network concentration .
- Software bugs and consensus forks: protocol implementation errors or contentious upgrades can produce accidental chain splits or force-rollbacks if not managed with strong governance .
- Off-chain data manipulation & oracle risk: anchoring or referencing external records (e.g.,supply chain manifests,medical metadata) exposes the system to tampering where the on-chain pointer remains immutable but the referenced truth is altered .
- Key compromise and social engineering: loss or theft of private keys,compromised custodians,or targeted attacks on custodial providers can make records effectively reversible from the user viewpoint.
Practical mitigations reduce these risks and preserve the ledger’s practical immutability. Key controls include:
- Decentralization & economic security: maintaining a broad base of miners/validators and high participation raises the cost of any reorganization attempt .
- Robust software governance: formal verification, multi-client implementations, public code audits and slow, well-governed upgrade processes limit consensus-breaking bugs .
- On-chain anchoring and provenance: use merkle proofs, timestamping and multiple independent oracles to validate off-chain facts and reduce single-point trust .
- Key-management best practices: multi-signature custody, hardware security modules, air-gapped signing and rigorous operational procedures protect against human compromise.
| Threat | Primary Mitigation |
|---|---|
| Majority-hash control | Wider decentralization; economic disincentives |
| Off-chain tampering | Multiple oracles; on-chain anchoring |
| Custodian/key loss | Multi-sig; HSMs; custody audits |
Operational guardrails for organizations include adopting interoperable standards, participating in multi-stakeholder governance forums, regular independent audits and transparent incident response plans - measures promoted by cross-sector initiatives that accelerate responsible blockchain use and trust in applications from finance to supply chains and healthcare .
Legal and forensic implications of immutable records in dispute resolution
Immutable records on bitcoin mean transactions and timestamps are intended to be resistant to alteration, a core principle described by standard definitions of immutability as being incapable of change or not able to be altered . In legal proceedings this permanence can confer strong evidentiary value: courts may treat blockchain entries as robust logs of intent, transfer, or chronology, but that value is conditional on proper authentication and context. Key legal considerations include:
- Evidentiary weight: immutable ledgers can strengthen chain-of-custody arguments when cryptographic provenance is demonstrable.
- Data protection conflicts: permanent records can clash with privacy rights or directives such as the right to be forgotten, requiring redaction strategies or legal balancing tests.
- Jurisdictional acceptance: admissibility varies by court and jurisdiction; procedural rules still govern how blockchain evidence is introduced and explained to factfinders.
From a forensic perspective, immutability provides reliable cryptographic anchors-hashes and timestamps that forensic analysts use to correlate events and validate file integrity-but it does not replace investigative rigor. analysts must authenticate keys, trace on-chain-to-off-chain linkages, and demonstrate that on-chain records accurately reflect contested real-world transactions; immutability guarantees that a recorded datum cannot be changed after inclusion, but it does not vouch for the correctness of what was originally recorded . Practical steps for dispute resolution combine technical and legal workflows: preserve raw blockchain evidence, engage qualified cryptographic experts, and prepare clear chain-of-custody documentation so judges and juries can evaluate both the immutability and the provenance of contested records.
Practical allocation of responsibilities:
| Stakeholder | Recommended action |
|---|---|
| Forensic analyst | Validate hashes and link to source systems |
| Litigators | Frame admissibility and privacy mitigations |
| Organizations | Adopt retention policies and demonstrable consent records |
Best practices for custodians and exchanges to respect and leverage blockchain immutability
Adopt immutability-first operational rules that treat on-chain records as the canonical source of truth: design settlement flows to prefer on-chain finality, publish cryptographic proofs for user balances, and avoid backdated off‑chain ledger edits. Practical steps include:
- use verifiable proofs-of-reserve and Merkle proofs for account reconciliations;
- commit transactional metadata on-chain when privacy allows;
- document and publish an immutable audit trail for policy changes.
These measures reinforce transparency and interoperability expectations promoted by global blockchain governance initiatives and help custodians demonstrate that they respect the ledger’s finality .
Operational controls must complement cryptography: enforce multi‑signature policies,isolate keys in hardware Security Modules (HSMs),rotate keys with verifiable on‑chain key‑announcements,and require dual approval for sensitive withdrawals. When human error or legal constraints require corrective action,prefer compensating on‑chain transactions and transparent user notifications rather than attempting to rewrite history; leverage blockchain analytics and traceability tools to forensically track flows and prove corrective steps. Real-world use cases - from food supply traceability to securing healthcare records – show how immutable ledgers improve accountability while minimizing systemic risk when custodians design processes around immutability rather than against it .
| Practice | Primary Benefit |
|---|---|
| On‑chain settlement where possible | Undeniable finality |
| Multi‑sig + HSM key custody | Reduced single‑point compromise |
| Public cryptographic proofs | Verifiable transparency |
Auditability and governance are the final pieces: require routine third‑party on‑chain audits, publish APIs for independent verification, and participate in multi‑stakeholder governance frameworks to align legal and technical practices with the ledger’s immutable nature. These steps build user trust and ensure exchanges and custodians harness immutability as a strength rather than a constraint .
Future developments affecting immutability and actionable steps for stakeholders
bitcoin’s core guarantee of permanent records will continue to face evolving pressures from both technology and policy. Quantum-capable adversaries, concentrated mining power enabling deep reorgs, and legally compelled changes to infrastructure all present realistic vectors that could erode effective immutability unless anticipated and mitigated. recent analyses of future threats and proposals for maintaining tamper-resistance underscore that immutability is robust but not immutable against every future development .
- Quantum risk: prepare cryptographic agility and migration plans.
- Concentration risk: encourage decentralization of mining and relay networks.
- Regulatory pressure: develop transparent custody and compliance models.
- Protocol evolution: prefer upgrades that preserve strong verification guarantees.
Stakeholders can take concrete, immediate steps to shore up immutability in practice. Developers and protocol designers should emphasize backward-compatible, well-audited upgrades; node operators and businesses must run and support a diverse set of full nodes; custodians and enterprises should maintain auditable off-chain records and multi-party custody to protect against single points of failure. Practical assignments are summarized below for quick reference, drawn from recent technical and policy literature on blockchain mutability and mitigation strategies .
| Stakeholder | Priority Action |
|---|---|
| Miners | Distribute infrastructure across jurisdictions |
| Node operators | Run full nodes and enable independent validation |
| Developers | Audit upgrades and preserve verification paths |
| businesses | Implement off-chain proofs and custody diversification |
Long-term resilience depends on continuous monitoring, community governance, and retaining the technical means to prove history (e.g., Merkle proofs, archival nodes). stakeholders should institutionalize monitoring for atypical chain reorg activity, invest in cryptographic research to prepare for post-quantum transitions, and design policy responses that respect the protocol’s verification model while addressing legitimate legal requirements. These combined technical and governance measures preserve the practical immutability that bitcoin relies on, even as external pressures evolve .
- operational best practice: run and monitor full nodes; keep independent backups.
- Technical best practice: design for cryptographic agility and transparent upgrade paths.
- Governance best practice: foster decentralized decision-making and clear legal policies.
Q&A
Q: What does “immutable” mean in the context of bitcoin’s blockchain?
A: Immutable means that once data (transactions and block records) is written into bitcoin’s blockchain it cannot be changed or erased by any single participant; the ledger is designed to be tamper-resistant so past records remain intact and verifiable over time .Q: how does bitcoin’s blockchain create that immutability?
A: Immutability arises from a combination of cryptographic hashing (each block references the previous block’s hash), proof-of-work consensus (miners expend computational effort to add blocks), and decentralization (many independent nodes store and validate the ledger). Altering a past block would require redoing proof-of-work for that block and all subsequent blocks and getting a majority of the network to accept the changed chain .
Q: Why is cryptographic hashing vital to immutability?
A: Each block includes a hash that summarizes its data; because hashes are sensitive to any change, modifying a single transaction changes the block’s hash, which breaks the chain unless all later blocks’ proofs-of-work are recomputed. This linkage makes undetected tampering computationally impractical .Q: What role does proof-of-work play in preventing alterations?
A: Proof-of-work requires significant computation to produce a valid block. To alter history an attacker must redo the proof-of-work for the altered block and every block after it and outrun the honest network-an effort that generally becomes prohibitively expensive as more blocks are built on top of the target block .
Q: Can blockchain immutability be absolute, or are there limits?
A: Practically immutable: bitcoin’s design makes changes extremely difficult but not theoretically impossible. Short reorganizations can occur, and very powerful attackers (e.g., controlling a majority of hashing power) could rewrite recent history. In practice, the longer a transaction has been confirmed (more blocks built on top), the more secure its immutability becomes .
Q: What is a 51% attack and how does it affect immutability?
A: A 51% attack happens when one actor or colluding group controls a majority of mining/hash power. They could potentially reorganize the chain to double-spend or replace recent blocks. This undermines practical immutability for the affected time span, though executing and sustaining such an attack on bitcoin is resource-intensive and detectable .
Q: How many confirmations are considered safe to assume a bitcoin record cannot be altered?
A: There is no single universal number, but conventionally 6 confirmations (about one hour) is treated as strong finality for many transactions. Higher-value transactions may wait for more confirmations; security increases with each additional block because the cost of reversing the chain grows rapidly .
Q: Can protocol changes (forks) alter past records?
A: Forks (soft or hard) change consensus rules going forward; they do not retroactively rewrite historical block contents. Though, a contentious hard fork can split the network into separate ledgers with different histories for blocks after the fork point. Forks are governance and upgrade mechanisms, not simple ways to edit old transactions .
Q: Are records on bitcoin’s blockchain legally immutable?
A: Technical immutability (resistance to alteration within the network) is not the same as legal permanence. Courts, regulators, or custodians can require off-chain remedies (e.g., court orders, account freezes at custodians) that affect real-world consequences, but they cannot technically alter on-chain transaction history unless changes are coordinated via network consensus or other mechanisms .
Q: How can anyone verify that a transaction is recorded and immutable on bitcoin’s blockchain?
A: use a blockchain explorer to look up a transaction ID or address and see its inclusion in a block plus the number of confirmations. Public explorers and full nodes provide the same underlying verifiable data; explorers offer a user-kind interface for checking transaction status and block confirmations .
Q: What practical benefits does blockchain immutability provide?
A: immutable records enhance trustless verification (anyone can check history), reduce the need for third-party recordkeepers, improve auditability, and protect against retroactive tampering-useful for financial settlement, proof-of-ownership, and audit trails among other use cases .
Q: What are common misconceptions about immutability?
A: Misconceptions include believing immutability is absolute and instantaneous.In reality, immutability is probabilistic-security grows over time with confirmations. Another misconception is that immutability prevents any corrective action; off-chain governance, custodial reversals, and social or legal interventions can still affect outcomes even if on-chain data remains unchanged .
Q: could governments or organizations force changes to the blockchain?
A: Governments can pressure custodians, exchanges, or developers, and could attempt to censor or regulate crypto infrastructure. However, forcing a change to bitcoin’s immutable ledger would require either controlling a majority of mining power or convincing a majority of the network to accept a protocol change; both are technically and politically difficult at scale .
Q: Are there trade-offs associated with designing for immutability?
A: Yes. Strong immutability via decentralized proof-of-work increases resource use (energy and hardware), slows transaction finality compared with some centralized systems, and makes correcting accidental or fraudulent on-chain actions difficult. These trade-offs reflect design choices between censorship-resistance, security, and flexibility .
Q: How does bitcoin’s immutability compare to other blockchains or databases?
A: bitcoin emphasizes robust, long-term immutability through proof-of-work and wide decentralization. Other blockchains may use different consensus (e.g., proof-of-stake) or permissioned models that trade some decentralization for faster finality or governance flexibility; conventional databases offer easy reversibility and stronger administrative control but lack the same public verifiability and censorship resistance .
Q: What should users do to rely on bitcoin’s immutability safely?
A: Use standard security practices: confirm sufficient block confirmations before treating transactions as final, verify transaction details before sending, back up private keys, and use reputable wallets or full-node verification for high-value transactions. For verification, consult reliable blockchain explorers or run a personal node to independently validate history .
Q: Can on-chain metadata or side-layer systems undermine immutability?
A: On-chain metadata is part of the blockchain and inherits its immutability properties. Side layers or off-chain systems that reference bitcoin can have their own rules and risks; their records may not be as immutable as bitcoin’s base layer and can be subject to their own governance or technical vulnerabilities .
Q: Where can readers learn more about bitcoin’s blockchain and explore records themselves?
A: Authoritative explainers on how blockchains work and their characteristics provide technical background and context . To inspect real transactions and blocks, use a public explorer such as blockchain.com’s explorer to search transaction IDs, addresses, and block data .
In Retrospect
bitcoin’s immutability-rooted in cryptographic hashing, block linking, and decentralized consensus-means that once transactions are confirmed and recorded on the chain they cannot be altered without detection, providing a durable and auditable ledger of value transfers.Public tools and documentation make this property verifiable: anyone can inspect transactions and blocks through blockchain explorers and review how transactions are constructed and confirmed to understand why alterations are infeasible . Ongoing on‑chain charts and data further demonstrate the transparency and measurable activity of the network, reinforcing the practical implications of that immutability for users, auditors, and developers alike .