Headlines about dramatic price moves,security risks and market drama can make bitcoin seem like a force driven by a single hand,but that impression masks a different reality.bitcoin recently drew fresh attention when its price surged past $120,000, a reminder of how quickly headlines can shift market focus . Simultaneously occurring, conversations about vulnerabilities – from theoretical quantum attacks to broader critiques of the crypto ecosystem – underscore why understanding bitcoin’s governance is critically important for assessing its resilience and future direction .
Contrary to the idea of centralized control, bitcoin’s authority rests on distributed consensus: a set of open rules and the collective choices of software developers, node operators, miners or validators, exchanges and users. Changes to the protocol require broad agreement across these self-reliant actors,and real-world control is exerted through adoption,enforcement and economic incentives rather than by any single company,government or individual. This article explains how that consensus mechanism works in practice, who the main participants are, and how bitcoin’s decentralized governance responds to technical risks and market pressures.
Understanding bitcoin’s Governance Model: Consensus Mechanisms and Distributed Decision-Making
bitcoin’s operating code is the constitution – a set of consensus rules embedded in open-source software that every participant can run and inspect. No single company or government can unilaterally change those rules; rather, changes require broad technical and economic acceptance from the network of users and node operators who validate transactions and blocks. This rule-enforcement model makes bitcoin a permissionless, decentralized system where the protocol’s state is determined by the highest level of agreement across independently running software implementations .
Proof-of-Work (PoW) is the primary consensus mechanism securing bitcoin: miners expend computational effort to propose new blocks,and the network accepts the longest valid chain as canonical. That competition both orders transactions and provides economic incentives for honest behavior, but it also creates measurable electricity demand because of the energy-intensive mining process. Discussions about governance thus frequently enough intersect with debates over mining centralization and resource use, which affect both security and public perception .
Decision-making is distributed and multi-layered: software developers propose improvements, miners signal support by upgrading mining software, and full nodes ultimately enforce which rules are accepted by refusing invalid blocks. Major changes typically require either backward-compatible soft forks (adopted gradually) or contentious hard forks (splitting the chain if consensus fails). Critics sometimes characterize cryptocurrencies as scams or centralized schemes, but those critiques overlook how governance in bitcoin emerges from economic incentives and decentralized enforcement rather than from a single controlling party .
Key actors and their practical influence include an ecosystem of independent participants. Consider this concise view:
- Miners – produce blocks and secure the chain.
- Full nodes – validate rules and reject invalid history.
- Developers - propose protocol changes via open-source code.
- Users - choose wallets, exchanges, and whether to adopt upgrades.
| Actor | Primary Role | Influence |
|---|---|---|
| Miners | Secure & add blocks | High (economic) |
| Full nodes | Enforce rules | High (validation) |
| Developers | Design upgrades | Medium (technical) |
| Users | Adopt or reject | Variable (market) |
Who Actually Influences bitcoin: Roles of Miners, Full Nodes, developers, Exchanges and Users
Miners secure bitcoin by expending energy to produce blocks, capturing block rewards and fees as their incentive; they can temporarily reorder or withhold transactions they mine but cannot unilaterally change protocol rules. Full nodes enforce the rules by validating transactions and blocks, rejecting invalid data and relaying valid information across the network.
- What miners can do: prioritize fees, choose which transactions to include.
- What full nodes can do: decide which consensus rules to enforce and which software version to run.
- What neither can do alone: rewrite history beyond consensus limits or change consensus rules without broad coordination.
Developers write, review and maintain bitcoin client implementations; they craft proposals (BIPs) and fixes that shape future behavior but cannot push changes without node and miner adoption. Developers are the primary line of defense for protocol-level security and upgrades – such as, emerging threats such as quantum-capable attacks drive research and potential upgrade pathways that developers must coordinate on and test before deployment .
- propose code changes, perform audits and run reference implementations.
- publish releases; adoption depends on the wider ecosystem.
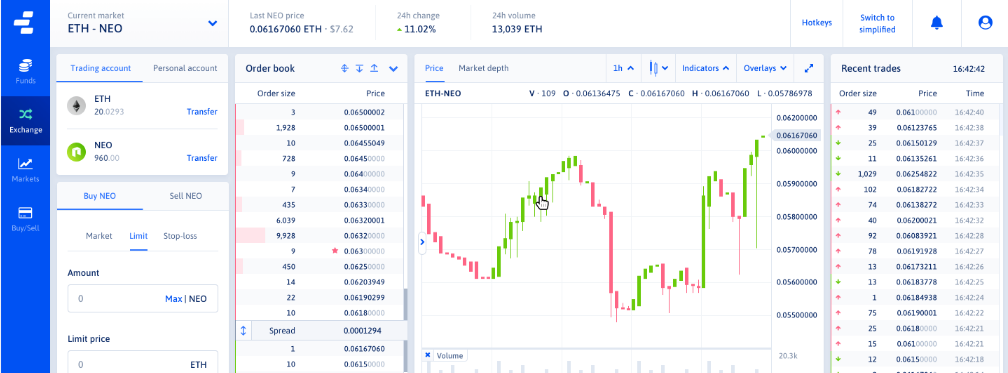
Exchanges and custodial services influence liquidity, on‑chain demand and price finding by making access easier for many users; wallet choices shape custody models and user security practices – wallet comparisons and custody options are central to how people interact with bitcoin and with broader market flows . Market sentiment and macro narratives propagated by media and trading platforms also amplify price moves and participation cycles . Below is a concise reference of key actors and their primary levers:
| Role | Primary Influence | Typical Action |
|---|---|---|
| Miners | Block production | Prioritize fees |
| Full nodes | Rule enforcement | Validate & reject |
| Developers | Protocol evolution | Propose/patch code |
| Exchanges | Liquidity & access | Custody & listing |
| Users | Adoption & choice | Run nodes, choose wallets |
Ultimately, control is emergent: consensus arises from the interplay of incentives, software choices and economic behavior rather than a single actor. Key checks and balances include community review of code, economic incentives that align honest participation, and the voluntary adoption of software by node operators and miners.
- Economic checks: miners and exchanges risk capital if they act against network interests.
- Technical checks: full nodes prevent invalid rules from taking effect by refusing to follow them.
- Social checks: community coordination and reputational forces constrain unilateral change.
How Consensus Is Reached in Practice: Soft Forks, Hard Forks and Client Adoption Dynamics
bitcoin protocol changes move through two technical paths: soft forks, which are backwards-compatible rule tightenings, and hard forks, which create new, incompatible rulesets. Soft forks allow upgraded nodes to enforce stricter validation while older nodes still accept the new blocks, so the network can tighten behavior without an immediate split. Hard forks require a coordinated upgrade because nodes that don’t adopt the new rules will reject blocks from upgraded nodes,ofen producing two competing chains if coordination fails.
Actual upgrades are as much social processes as technical ones. Miners, full-node operators, wallet providers, exchanges, and developers each play distinct roles in adoption. Key dynamics include miner signaling, client releases, and user/enterprise migration. Typical stakeholders are:
- Miners: validate blocks and can influence short-term activation through signaling.
- Node operators: enforce consensus rules and determine whether a change is accepted by the running network.
- Service providers: (wallets, exchanges) that decide when to support a new chain or client.
- Developers & community: draft proposals (BIPs), coordinate testing and interaction.
Coordination outcomes can be summarized simply:
| Change | Compatibility | Typical Result |
|---|---|---|
| Soft fork | Backwards-compatible | Single chain if miners/nodes adopt |
| Hard fork | Non-compatible | Risk of chain split without consensus |
Beyond code, external forces-regulatory pressure, market incentives, and infrastructure costs-shape adoption. Large-scale mining operations, which consume notable electricity and are sensitive to policy, can affect signaling behavior and deployment timelines. Likewise, shifts in political or economic sentiment influence which clients and services prioritize support for upgrades, a dynamic discussed in broader market outlooks. Ultimately, consensus in bitcoin emerges from layered technical rules plus collective human coordination, not from any single controlling party.
Measuring Decentralization: Metrics and Tools to Monitor Network Health and Concentration Risks
Quantifying decentralization requires a clear taxonomy of signals: governance (who can change rules), execution (who validates blocks), and economic concentration (who holds and can move value). These axes make decentralization measurable rather than purely rhetorical.Measuring each axis with objective indicators turns a philosophical debate into an operational dashboard-mirroring how modern organizations rethink distributed operations to avoid single points of failure and how resilient infrastructures require distributed controls and visibility .
Core on-chain metrics and the tools that surface them:
- Nakamoto coefficient – number of independent entities required to disrupt consensus; low values indicate high systemic risk.
- Hashrate / Validator share - distribution of mining or staking power across pools or validators; visualized by blockchain telemetry.
- Wealth concentration (Gini / top‑k wallets) – distribution of coin ownership and potential for large market-moving actions.
- Client and software diversity – diversity of node implementations to detect single‑bug failure modes.
- Node geography & connectivity – AS/BGP and latency maps revealing network partition or regional choke points.
Practical tooling includes on‑chain analytics platforms and network scanners that export these indicators into time series for trend analysis; concentration mirrors risks seen in global supply chains when a few actors become single points of failure .
Off‑chain dependencies demand equal attention: mining pool coordination, custodial exchange balances, and developer repository control are external factors that amplify centralization even when on‑chain figures look healthy. Monitorable signals include:
- Exchange custody ratios – percent of circulating supply held on custodial platforms.
- Mining pool coordination events – sudden merges/splits or signaling behavior.
- Repository commit authorship - concentration of active maintainers on protocol code.
| Metric | What it flags |
|---|---|
| Nakamoto coefficient | Consensus fragility |
| Top‑10 wallets | Market manipulation risk |
| Client diversity | Implementation single‑point failures |
Interpreting measurements requires context and continuous monitoring: single snapshots can be misleading-seasonal miner migrations, market cycles, or protocol upgrades temporarily skew numbers. Use rolling windows, correlate on‑chain and off‑chain indicators, and set alert thresholds (for example, a Nakamoto coefficient under four or top‑5 pools >50% of hashrate should trigger review). Ultimately, decentralization is an operational state to maintain, not a binary outcome, and best practices from decentralized industrial systems and grid design reinforce the need for automated observability and governance playbooks .
reducing Centralization Risks: Practical Recommendations for Node Operators, miners and Service Providers
Node operators should prioritize heterogeneity and independence to keep the network resilient. Run and maintain a local full node, choose from multiple client implementations, and prefer diverse hosting providers across different jurisdictions. Practical steps include:
- Run multiple clients (e.g., bitcoin Core and an alternative) to avoid single-client monoculture.
- Geographic distribution of nodes to reduce regional outages and regulatory choke points.
- Use independent peers and avoid relying solely on centralized DNS seeds or single upstream providers.
These measures help prevent a concentration of validation or propagation paths that could be exploited by policy shifts or coordinated attacks .
Miners play a critical role in decentralization beyond hashing power. To limit pooling centralization, miners should prioritize transparent, permissionless block template policies and consider joining or creating smaller, cooperative pools that enforce anti-censorship rules. Encourage frequent publication of mining firmware and relay policies, and independently verify block templates before signing blocks. Such operational openness reduces single-point influence and makes it harder for external actors to coerce coordinated behavior – an important consideration as state and policy actions around crypto evolve .
Service providers – exchanges, custodians, wallets and relays – should adopt standards that empower users and reduce custodial concentration. Offer non-custodial options, open APIs, and client-side key management; avoid defaulting users into custodial models. Implement privacy-conscious defaults and clear documentation about transaction traceability,as perceived anonymity differs from technical reality and can affect user behavior and regulatory responses . Regular independent audits, proof-of-reserves (with privacy-preserving techniques), and interoperability with diverse node implementations strengthen ecosystem trust without centralizing control.
Operational hygiene and community collaboration lock in long-term resistance to centralization. Maintain timely, well-tested update practices, publish reproducible builds, and engage in open governance discussions with othre operators. The table below summarizes simple, high-impact actions and their primary benefits for quick reference:
| Action | Primary Benefit |
|---|---|
| Run a local full node | Independent validation |
| Diversify mining pools | Reduces single-pool control |
| Offer non-custodial services | User sovereignty |
| Publish reproducible builds | Software integrity |
Collectively, these practices foster a system where consensus rules – not any single entity – determine bitcoin’s state.
Economic Forces That Shape Protocol Changes: Incentives, Market Power and Fee markets
Economic incentives are the engine behind any protocol change proposal. Miners and validators respond to reward structures (block subsidy + fees), users react to transaction costs and confirmation times, and developers calibrate upgrades around who pays for research and who benefits from adoption. typical incentive drivers include:
- direct revenue: block rewards and fee capture that shape miner behavior.
- User demand: willingness to pay for faster or cheaper transactions.
- Developer incentives: reputation, grants, or ecosystem growth that fund changes.
Market power concentrates influence even in permissionless systems when economic actors grow large. Mining pools, major exchanges and, occasionally, nation-states can sway deployment timing or adoption by creating de facto coordination points. High-level interventions – including reported government interest in large-scale bitcoin holdings - illustrate how external actors can alter perceived incentives and market signaling around protocol choices . Likewise, recurring losses from fraud and scams reshape user behavior and centralize reliance on custodial services, which in turn affects which changes gain traction in the ecosystem .
Fee markets are the on-chain auction that determines how scarce block space is allocated. When demand spikes, fees rise, changing user strategies, altering mempool dynamics and incentivizing miners to prioritize transactions that pay more.Fee design proposals - from dynamic block limits to fee-burn mechanisms – are responses to these market signals. Security considerations also feed into economic choices: novel threats or changing risk profiles (such as, emerging cryptographic risks) can accelerate consensus around upgrades to protect value and maintain trust .
| Stakeholder | Primary Economic Lever |
|---|---|
| Miners | Block selection & fee capture |
| Users | Fee bidding & demand |
| Exchanges/Wallets | Custody & liquidity provisioning |
Protocol change outcomes reflect the equilibrium of these incentives: no single entity dictates direction – economic forces, not fiat authority, shape which proposals survive and gain consensus.
Regulatory Pressures and Institutional Influence: How Stakeholders Can Prepare and Respond
Regulatory frameworks shape how market participants operate, but they do not substitute for bitcoin’s underlying consensus rules; laws set broad objectives while regulations provide the technical steps to meet them, which is why understanding the distinction matters for planning compliance and product design . Regulators can influence access, custody, and on‑ramping to the network through licensing, reporting and enforcement actions without changing protocol consensus, so stakeholders must treat regulation as an operational constraint rather than a layer that controls the blockchain itself.
Planning is operational and legal. Entities that interface with fiat or customers should prioritize practical controls and governance; key preparedness actions include:
- Robust compliance programs - KYC/AML, recordkeeping, and transaction monitoring.
- Transparent governance – clear policies for upgrades, custody and dispute resolution.
- Legal & policy engagement – regular counsel and dialog with regulators.
- Technical resilience – redundancy, secure custody, and auditability of processes.
These measures must be tailored by jurisdiction and sector because regulatory compliance varies by industry and location, affecting banks, exchanges, custodians and research differently .
Practical responses span advocacy, technical design and corporate policy. Regulators - understood as bodies that set and enforce rules governing behavior - impose requirements that firms must adapt to while preserving decentralization where possible .A compact reference for stakeholders:
| Stakeholder | Primary Response |
|---|---|
| Exchange | Licensing + enhanced AML/KYC |
| Miner/Pool | Geographic risk diversification |
| Wallet Provider | User education + non‑custodial options |
| Institutional Investor | Custody audits + regulatory reporting |
ultimately, regulatory pressure and institutional influence shape the ecosystem around bitcoin but do not replace consensus as the mechanism that controls protocol state; stakeholders who combine compliance discipline, technical best practices and active policy engagement will be better positioned to operate within regulatory regimes while supporting a resilient, decentralized network .
Recommendations for Long-Term Resilience: Technical, Economic and Governance Actions to Preserve Consensus
Harden the protocol stack by prioritizing backward-compatible upgrades, rigorous testnets and diverse client implementations so that no single software bug or client maintainers can steer consensus. Encourage independent implementations and fuzz-testing programs, maintain cryptographic agility for future-proofing, and support BIP-style improvement proposals that include formal verification where feasible. Contrast this distributed approach with centralized authentication systems to illustrate the risk of single points of control in permissioned environments: centralized portals emphasize single-credential trust, which bitcoin explicitly avoids .
Align economic incentives to preserve long-term miner, node, and user participation. Policies should promote a healthy fee market, reduce reliance on temporary block subsidies, and lower barriers to running validating nodes. Recommended actions include:
- diversify mining infrastructure and support pool competition;
- design fee mechanisms that reward long-term security;
- promote noncustodial wallet adoption and clear custody best practices;
- incentivize full nodes through lightweight UX and resource optimizations.
These measures help prevent concentration of economic power that would otherwise mimic centralized access management models used by institutional systems .
Strengthen governance processes with transparent upgrade pathways, documented veto and emergency procedures, and broad community review windows. The following simple roadmap clarifies responsibilities and expected outcomes for on-chain and off-chain coordination:
| Action | Short example |
|---|---|
| Proposal review | 30-90 day public audit |
| Testing | Multi-client testnet run |
| Signaling | GRS-style opt-in signaling |
| Emergency response | Pre-agreed rollback limits |
Operationalize monitoring and dispute resolution by funding independent observability (network health dashboards, chain analytics) and creating clear, lightweight dispute-resolution forums for contentious upgrades. Run regular cross-client interoperability drills, keep upgrade timelines predictable, and document fallback behaviors so users and custodians can respond consistently. Use lessons from centralized login and admin systems to emphasize clear access control boundaries and audit trails without central authority dependence .
Q&A
Q: Who “controls” bitcoin?
A: No single person, company, or government controls bitcoin. Control is distributed across participants who follow and enforce the protocol’s rules – primarily full nodes, miners/validators, developers, exchanges, and users. Changes to bitcoin’s rules require broad agreement among these groups; otherwise, competing versions (forks) can split the network.
Q: What does “consensus” mean in the context of bitcoin?
A: Consensus means the network participants independently validate and accept the same set of rules and transaction history. bitcoin’s consensus combines cryptographic proof-of-work,node validation,and social agreement: miners produce blocks,full nodes verify blocks and transactions,and the community adopts software that enforces the accepted rules.
Q: Who enforces bitcoin’s rules?
A: Full nodes enforce the rules by rejecting blocks and transactions that violate the protocol. Miners produce candidate blocks, but full nodes ultimately decide whether those blocks are valid. Developers produce software implementations, but node operators choose which implementation and version to run.
Q: Can miners unilaterally change bitcoin?
A: Not without broader support. Miners can attempt to impose changes by controlling a majority of hashing power,but miners alone cannot compel users and full nodes to accept rule changes. A change that requires different block validation (a “hard fork”) needs coordinated adoption by nodes, wallets, exchanges, and users to become the dominant chain.
Q: What is a hard fork vs a soft fork?
A: A hard fork introduces changes incompatible with previous rules; nodes that don’t upgrade will be on a separate chain. A soft fork is backward-compatible: upgraded nodes can enforce new, tighter rules while older nodes still accept the new chain. Hard forks therefore require stronger social and technical coordination to avoid chain splits.
Q: Could a 51% attack let someone “control” bitcoin?
A: A miner (or coalition) with 51%+ of hashing power can reorganize recent blocks,double-spend transactions,and censor transactions for a time,which is serious but temporary. Such an attacker cannot change bitcoin’s protocol rules or steal coins from addresses without private keys; long-term control still depends on broader network responses.
Q: Do developers control bitcoin?
A: Developers maintain and propose changes to bitcoin’s reference implementations,but they do not have unilateral control. Their influence depends on the quality of code, community trust, and whether node operators and miners adopt their software.Ultimately, control is dispersed across those who run nodes and accept blocks.
Q: What role do exchanges and custodians play?
A: exchanges and custodial services control coins held on behalf of users and can affect liquidity, pricing, and user access. Large custodians or coordinated exchanges can exert market influence, but holding coins or listing policies does not change the underlying bitcoin protocol.
Q: Can governments control bitcoin?
A: Governments can regulate on-ramps and services (exchanges, banks, custody), seize coins held by entities under their jurisdiction, or even create policy that discourages use.They can also acquire and hold bitcoin (for example, some governments or agencies may hold seized coins or create reserves) but owning coins does not give them direct control over the decentralized protocol itself .
Q: Is bitcoin anonymous, and does that affect who controls it?
A: bitcoin transactions are pseudonymous and recorded on a public ledger; they are not wholly anonymous. The transparency of the ledger means actions and flows can be traced, which increases the ability of exchanges, investigators, and regulators to monitor activity – but it doesn’t centralize protocol control .
Q: If critics say bitcoin is a scam or controlled by insiders, is that true?
A: Critics sometimes describe crypto products, stablecoins, or NFTs as risky or subject to scams. While scams and failures exist in the broader crypto ecosystem, bitcoin’s control structure – a distributed consensus of nodes, miners, and users - makes it resilient to single-party control.Criticisms about scams tend to refer to specific projects or uses, not the consensus mechanism itself .
Q: What happens if there is a major disagreement about changing bitcoin?
A: Major disagreements can lead to contentious forks, where two incompatible chains continue separately and holders on each chain keep coins on that chain. Successful changes typically require broad coordination among developers,miners,node operators,exchanges,and the user community to avoid splits.
Q: In practice, who has the most influence?
A: Influence is distributed but some actors can have outsized practical influence: large mining pools (hashrate), popular full node implementations, major exchanges and custodians, and active developer maintainers. Influence is exercised through adoption choices rather than formal authority.
Q: Bottom line – who controls bitcoin?
A: bitcoin is controlled by consensus – a decentralized combination of technical rules, node validation, miner block production, developer proposals, and social agreement among users.no single entity has absolute control; power resides in how the network’s participants choose to run and accept software and rules.
In Summary
In short, no single company, government, or individual ”owns” bitcoin – control is emergent and exercised through consensus among the network’s participants: full nodes that enforce the rules, miners that propose blocks, developers who maintain and update software, and users who choose which rules and implementations to run. This distributed model means changes to bitcoin’s protocol require broad agreement across these groups rather than unilateral action.
That said, real‑world forces shape how that consensus forms.Mining economics and concentration of hash power can influence block production and have drawn attention because of their large electricity use and policy implications . Likewise, while bitcoin transactions are pseudonymous, they are not fully private, and off‑chain actors (exchanges, custodians, regulators) affect how people interact with the system .
Understanding who controls bitcoin thus means recognizing a system governed by incentives, software, and collective agreement – a protocol where authority is diffuse, accountability is social and technical, and changes depend on consensus rather than command.