Understanding the Role of Seed Phrases in bitcoin Wallet Security
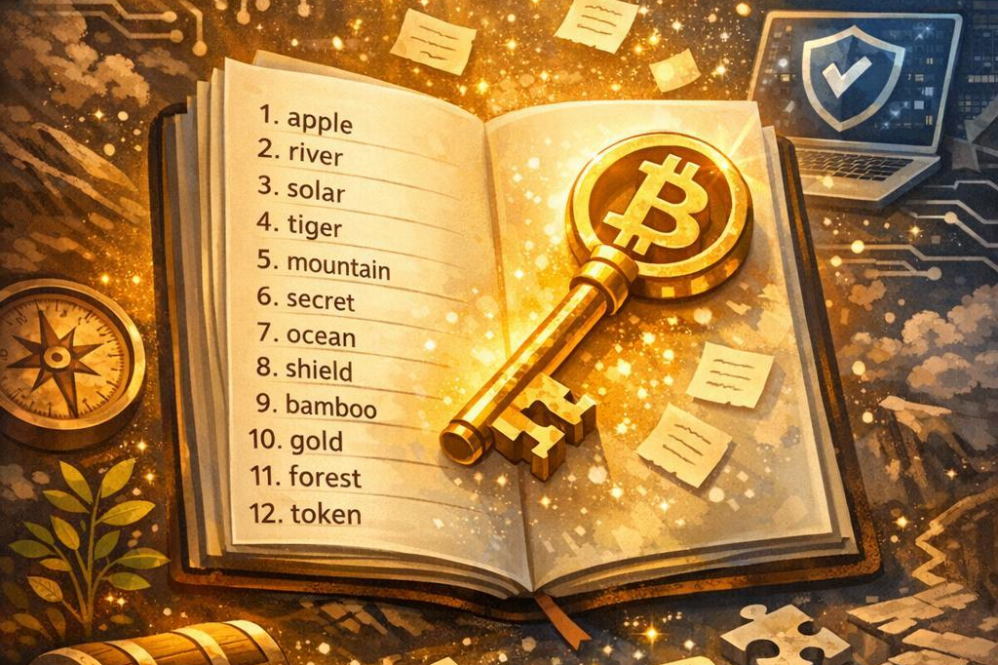
Seed phrases, sometimes called recovery phrases, are the cornerstone of safeguarding yoru bitcoin wallet. They consist of a sequence of seemingly random words-typically 12, 18, or 24-that act as the master key to your digital assets. This cryptographic backup allows users to restore full access to thier wallets if devices are lost, damaged, or compromised. Unlike customary passwords, seed phrases encapsulate the complex private key into an easier-to-store format, but demand utmost protection as anyone with access to the phrase controls the funds.
Security experts emphasize several best practices when handling these critical phrases:
- Write down and store offline: Digital copies are vulnerable to hacking; physical copies avoid such risks.
- Use multiple secure locations: Spread your backups to mitigate risks like theft or natural disasters.
- avoid digital transmission: Never share your seed phrase over email, chat apps, or cloud services.
| Feature | Purpose | Benefit |
|---|---|---|
| Human-readable words | Easier to memorize and record | Reduces recovery errors |
| Deterministic Wallet Generation | Creates multiple keys from one phrase | Consolidates wallet backups |
| Global Compatibility | Supports many wallet providers | adaptability in wallet restoration |
The Cryptographic Foundations Underlying Seed Phrase Protection
Seed phrases are not just random words; they are the backbone of bitcoin wallet security, grounded in complex cryptographic principles. At their core, seed phrases are generated using a process called deterministic wallet generation, which relies on a cryptographic algorithm known as the Hierarchical Deterministic (HD) Wallet standard (BIP-32 and BIP-39). This ensures that a single phrase can recreate an entire wallet’s private and public keys,providing a robust method for backup and recovery without compromising security. Each word is carefully chosen from a predefined list to maximize entropy while remaining user-kind.
The magic lies in the way these words encode entropy – a measure of randomness crucial for cryptographic security. When combined, seed phrases act as a master key, enabling users to recover their bitcoin wallets if devices are lost or damaged. This system is anchored by mathematical functions that create a secure yet reproducible path from mnemonic words to private keys. The underlying cryptographic hash functions and key derivation algorithms guarantee that without the exact phrase, it is indeed computationally infeasible for any attacker to guess or recreate the keys.
| Component | Role | Security Feature |
|---|---|---|
| Mnemonic phrase | Human-readable backup | Easy to write down & store securely |
| Seed Generation | Converts phrase to binary seed | Derives master key via PBKDF2 |
| Key Derivation | Creates private/public keys | Ensures wallet integrity & uniqueness |
By combining these cryptographic building blocks, seed phrases transform abstract mathematical principles into practical tools, bridging the gap between advanced security protocols and everyday usability. This fusion is what makes bitcoin wallet backup and recovery both accessible and incredibly resilient against threats.
Best Practices for Creating and Storing Seed Phrases Safely
When safeguarding your seed phrase, physical security is paramount. Rather than storing your seed phrase digitally, which leaves it vulnerable to hacking or malware, it is indeed best to write it down on durable materials such as metal plates or acid-resistant paper. These mediums withstand environmental hazards like fire and water better than standard paper. Additionally, consider dividing your seed phrase into parts and storing each segment in separate, secure locations for added protection against loss or theft.
employing a structured approach enhances security and accessibility. Such as, use a secured safe or a bank deposit box for primary storage, and share backup copies with trusted individuals only under strict terms. Avoid cloud storage or photographs on your phone, as these are common attack vectors. Below is a comparison of popular storage methods leveraging durability and security, helping you make informed decisions:
| Storage Method | Durability | Security Level | Risk Factors |
|---|---|---|---|
| Metal Plate Etching | High | Very High | Physical Theft, Fire |
| Paper in Fireproof Safe | Medium | High | Water Damage, Theft |
| Digital Note (Encrypted) | Medium | Medium | Hacking, Malware |
To maintain long-term integrity, regularly verify your seed phrase’s readability and condition. Periodic checks ensure that no degradation has occured to the physical medium and that the phrase remains accurate and complete. If you update or create a new wallet, generate a new seed phrase and securely destroy the old one to prevent unauthorized access.Maintaining strict confidentiality about your seed storage prevents social engineering attacks and inadvertent exposure to potential adversaries.
Common Vulnerabilities and How to Avoid Seed Phrase Compromise
One of the most critical risks to your bitcoin wallet’s security lies in the exposure of your seed phrase. Common vulnerabilities often stem from poor storage practices such as saving the phrase digitally without encryption or relying on cloud storage services that may be susceptible to hacking or leaks. Additionally, physical storage methods, if not carefully considered, can lead to loss or theft of the seed phrase. To mitigate these risks, always store your seed phrase offline in a secure and private location-preferably in a fireproof and waterproof container-and avoid any form of digital copying unless encrypted with robust security protocols.
Phishing attacks and social engineering tactics can also lead to seed phrase compromise. Attackers might impersonate wallet providers or support personnel to coax users into revealing their seed phrases. To defend against these threats, never share your seed phrase with anyone and verify the authenticity of any communication asking for sensitive information. Employing hardware wallets that do not reveal the seed phrase during normal transactions adds an extra layer of protection, as keys never leave the device.
| Vulnerability | Avoidance Strategy |
|---|---|
| Unencrypted Digital storage | Store seed phrases offline in secure physical forms |
| Phishing Attempts | Never disclose seed phrases; verify sources |
| Physical Theft or Damage | Use fireproof, waterproof storage solutions |
Step-by-Step Guide to Wallet Recovery Using Seed Phrases
Recovering a bitcoin wallet using seed phrases involves a systematic approach designed to ensure you regain access without compromising security. Begin by locating your seed phrase, which is typically a collection of 12 to 24 carefully ordered words generated during wallet setup. These words serve as the master key to your wallet’s private keys, making their accuracy paramount. Before attempting the recovery, ensure you are working in a safe and private habitat, free from prying eyes or malicious software.
Next, access the wallet application or hardware device where you intend to restore your funds. Most wallets feature an option like “Restore Wallet” or “Recover Wallet.” Upon selecting this, you will be prompted to enter your seed phrase, maintaining the exact order and spacing. Some platforms may also include verification steps or ask for additional security measures such as passwords or PINs. It’s essential during this process to enter the seed phrase precisely to avoid errors that could lead to irretrievable loss.
To aid in understanding the process, consider this simple checklist that outlines the critical steps of seed phrase recovery:
| Step | Action | Notes |
|---|---|---|
| 1 | locate Seed Phrase | must be exact 12-24 words |
| 2 | Open Wallet Recovery | Use official wallet app or device |
| 3 | Input Seed Phrase | Type carefully; order matters |
| 4 | Confirm & Secure | Verify recovery, set new security |
By following this clear, stepwise method, users ensure their bitcoin assets remain secure and accessible, emphasizing the critical role of seed phrases in wallet backup and restoration.
Advanced Recommendations for Enhancing Seed Phrase Backup Reliability
Utilizing multi-location storage for your seed phrase dramatically reduces the risk of complete loss due to localized disasters or theft. Consider securing copies in geographically dispersed, highly secure environments such as a safe deposit box, a trusted family member’s home, or an encrypted USB device stored separately. Redundancy paired with physical security is a foundational principle that prevents single points of failure in your backup strategy.
Another advanced technique is to split the seed phrase using a threshold secret sharing scheme-also known as shamir’s Secret Sharing. this method divides your seed phrase into parts, where only a subset (threshold) of those parts is needed to recover the full phrase.This approach means that even if one fragment is compromised,an attacker cannot reconstruct your entire seed phrase. implementing this requires careful management and distribution of shares among trusted parties.
Lastly, leverage tamper-evident physical mediums such as etched metal plates or cryptosteel backups, which withstand fire, water, and corrosion far better than paper. Durability extends the lifespan of your backup and ensures long-term access. Below is a comparison table to illustrate different backup mediums and their resilience factors:
| Backup Medium | Durability | Security Features | Recommended Use |
|---|---|---|---|
| Paper | Low | None | Short-term, low-risk environment |
| Metal Etching | High | Fire, Water, Corrosion Resistant | Long-term, high-value wallets |
| Encrypted USB | Medium | Password & Encryption | digital backup with physical separation |
| Shamir’s Secret Sharing | Varies | Distributed Trust & Partial Reconstruction | Maximum security & resilience |